Using Snake to Perform Malware Analysis
High level views
In Snake, we currently have four tabs available. The Details tab, shown below, will display the summary with details like the name, size and hashes, the hex dump and the integration with any ‘interface’ such as VirusTotal (VT) and Cuckoo. VT integration operates using a hash lookup function to allow hunters to know immediately whether the binary has been seen before and how it is classified. Cuckoo integration allows us to know whether the sample was previously uploaded to our internal Cuckoo instance.
The Notes tab allows us to easily share our findings across the team and collaborate on investigations.
The Interfaces tab is where you interact with other integrated tools. You can submit the sample to Cuckoo or see more details retrieved from VirusTotal.
The Analysis tab is where all the static goodness comes in and includes tools used to perform a wide variety of static analysis techniques. You can also add your own tools by creating a custom plugin (scale), which are basically simple Python wrappers for other programs.
Example Analysis
Imagine you are hunting through your estate and you find a suspicious service. How could we use Snake to analyse it? As an example, we’re going to walk through the process with the below service ‘SKLProService’.
The first step is to obtain a copy of the file and upload it to Snake.
With our file uploaded one of the first checks to perform is YARA scanning for known malicious indicators.
From the above hits, we now know the binary performs a type of process enumeration, checks for debugger presence, and calls Windows service functions.
We then check for the list of imports using pefile and can summarize the binary based on the DLLs loaded:
- The binary is not packed.
- USERENV.dll – contains functions to manage user profiles such as retrieving the environment variable.
- ADVAPI32.dll – provides access to advanced core Windows components such as the Service Manager and Registry.
- WTSAPI32.dll – contains functions to manage terminal services such as retrieving a list of RDP sessions.
- USER32.dll – contains user-interface components such as loading string resources from the executable.
- KERNEL32.dll – contains core Windows functionality such as access and manipulation of memory, files, and hardware.
Because Snake is a centralized storage platform, one of the advantages is we can perform fuzzy searches to look for any identical samples in our depository.
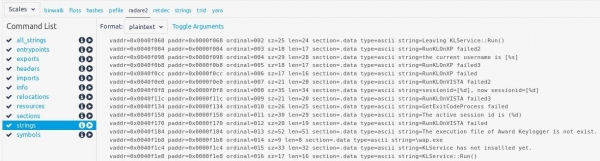
Even with the information we have on hand, it is still not conclusive. To learn more about the binary contents we can output strings using radare2. [1]
From the above output we see strings that reference a service ‘KLService::Run()’ and also a keylogger indicator ‘the execution file of Award Keylogger is not exist.’, which seems to be the ‘\wap.exe’.
vaddr=0x0040f23c paddr=0x0000f23c ordinal=020 sz=31 len=30 section=.data type=ascii string=CreateProcessAsUser failed(%d) vaddr=0x0040f25c paddr=0x0000f25c ordinal=021 sz=16 len=15 section=.data type=ascii string=winsta0\default vaddr=0x0040f26c paddr=0x0000f26c ordinal=022 sz=28 len=27 section=.data type=ascii string=DuplicateTokenEx failed(%d) vaddr=0x0040f288 paddr=0x0000f288 ordinal=023 sz=28 len=27 section=.data type=ascii string=OpenProcessToken failed(%d) vaddr=0x0040f2a4 paddr=0x0000f2a4 ordinal=024 sz=23 len=22 section=.data type=ascii string=OpenProcess failed(%d) vaddr=0x0040f2bc paddr=0x0000f2bc ordinal=025 sz=32 len=31 section=.data type=ascii string=GetExplorerProcessId failed(%d) vaddr=0x0040f2dc paddr=0x0000f2dc ordinal=026 sz=13 len=12 section=.data type=ascii string=explorer.exe vaddr=0x0040f2ec paddr=0x0000f2ec ordinal=027 sz=39 len=38 section=.data type=ascii string=Set Token Information value Error: %u\n vaddr=0x0040f314 paddr=0x0000f314 ordinal=028 sz=30 len=29 section=.data type=ascii string=Process token open Error: %u\n vaddr=0x0040f334 paddr=0x0000f334 ordinal=029 sz=30 len=29 section=.data type=ascii string=GetCurrentProcess failed(%d)\n vaddr=0x0040f354 paddr=0x0000f354 ordinal=030 sz=24 len=23 section=.data type=ascii string=dwSessionId value : %u\n
vaddr=0x0040f56c paddr=0x0000f56c ordinal=045 sz=9 len=8 section=.data type=ascii string=State:%d vaddr=0x0040f578 paddr=0x0000f578 ordinal=046 sz=18 len=17 section=.data type=ascii string=WinStationName:%s vaddr=0x0040f58c paddr=0x0000f58c ordinal=047 sz=14 len=13 section=.data type=ascii string=session_id:%d vaddr=0x0040f59c paddr=0x0000f59c ordinal=048 sz=26 len=25 section=.data type=ascii string=*****session %d********** vaddr=0x0040f5b8 paddr=0x0000f5b8 ordinal=049 sz=55 len=54 section=.data type=ascii string=----------------session infomation-------------------- vaddr=0x0040f5f0 paddr=0x0000f5f0 ordinal=050 sz=60 len=59 section=.data type=ascii string=WTSEnumerateSessions successfully, count of session is [%d]
Further on we see other indicators, such as process manipulation strings, which appear to be attempting to retrieve the explorer.exe process id, as well as creating processes as the user. It also appears to be retrieving a list of remote desktop sessions.
Summary
From the static analysis, we can conclude the binary is likely a GUI platform that has the ability to run functions, mainly around service manager, registry, terminal services, and memory and file manipulation.
However, the main keylogger binary should be wap.exe and it should be in the same directory.
Within a short amount of time we’ve gained a basic understanding of the binary and can share our findings with other team members using the notes feature. We’ve found Snake to be really useful both speeding up investigations and giving us better quality analysis overall – we hope it goes the same for you.
Snake by Countercept
https://github.com/countercept/snake
References
[1] https://rada.re
Categories